Man who drove car off cliff due in court ... Fire rips through Amityville home ... Trump on trial ... Lego camp
LONG ISLANDERS' FAVORITES
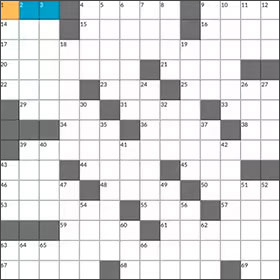
Newsday's daily crossword puzzle
Test your knowledge with Stan Newman's crossword.

Play Mahjongg Online
Play Mahjongg, everyone's favorite classic tile-matching game. Match tiles, clear the board and exercise your mind with Newsday.





